The current escalating tensions, in West Asia, focused on the Islamic Republic of Iran, began with the Assassination of Iran’s supreme leader, Ayatollah Ali Khamenei, in a joint Op codenamed “Epic Fury” conducted by USA & Israel. While it was precision attack targeting Iran’s supreme leader, alongside the strikes were a swell of cyber operations focused on Iran, ranging from the Prayer APP breach, further escalating the issue from within.
While we already know the Internet blockade of Iran well before the death of Khamenei and presently continuing to 168 hours with connectivity still flatlining around 1% of ordinary levels as indicated by Netblocks, while the only ones to retain access are officials and state media, the lauded digital Cage i.e. digital isolation did little to nothing to preventing IDF’s Unit 8200, from breaching the camera feeds of compound of Iran’s supreme leader.
The massive data mining and analysis allowed for the tracking of Khamenei, and once the CIA confirmed, the attendance of Iran’s senior leadership converging on his residence at Saturday, the decision was taken by U.S & Israel to execute the operation, Israel blocked dozen cell towers near Pasteur Street, essentially cutting of the security detail from receiving any warning of the impending attack on the compound. Israeli jets zeroed in and fired 30 precision munitions in daylight, a specific kind of missile called the Sparrow, variants of which are able to hit a target as small as a dining table from more than 1,000km away and executed the plan and took the targets out, the FT is said to have mentioned that the planning for the operation was on the books of Israel as far back as 2001 during the time of Ariel Sharon.
The following escalation after the death of Iran’s leaderships is having a ripple effect on the Middle East with the Strait of Hormuz, as the maritime seas are becoming a battlefield and Iran seems to want everyone to feel the strain of the conflict. The flow of Traffic density decreasing can been as under tracked by Marinetraffic the playback shows how density seems to decrease and traffic seems to hold to asses the situation.
Minimal vessel traffic seen in Strait of Hormuz amid reported closure
— MarineTraffic (@MarineTraffic) March 3, 2026
The latest #MarineTraffic playback shows visibly reduced transit density, alongside holding patterns, slower speeds, and vessels remaining outside the strait as operators reassess risk. pic.twitter.com/pfqk5rcbg8
The following escalation is continuing with the Strait of Hormuz, as the maritime seas are becoming a battlefield as Iran wants the world to feel the strain of the conflict, while the U.S seems to respond in kind, here U.S Centcom released footage of downing 20 Iranian Ship, lately adding a Soleimani-class warship to the list.Now coming to the Cyber aspect of the Iran Conflict or war, depending on which view one subscribes, the tactic employed by Israel was to not only breach systems to surveil Iran, but in theory alone it must have set up its own network relay’s to ensure the “digital Cage” would not effect their operations and to make use of native apps, to ensure it can conduct psyops among its citizens, in the aftermath of taking out the senior leadership of Iran. The Badesaba Prayer App hack, is, the app, was used by citizens of Iran to track prayer time’s and following the escalating conflict Push Notification showed were prompted via the app, which practically prompted the citizens to push onwards against the regime.
The Intention was simple, to further destabilize the local populus, and encourage those who are already strained under the current regime. This is but one example of the Cyber tactics employed by Israel against Iran.
Security analysts and researchers are presently predicting escalating attacks by Iranian Hacktivists against the large Middle East, targeted at Israel and then U.S. The target vector seems to be defence organizations,media outlets and Airports, some DDOS attacks while other detailed specific attacks.
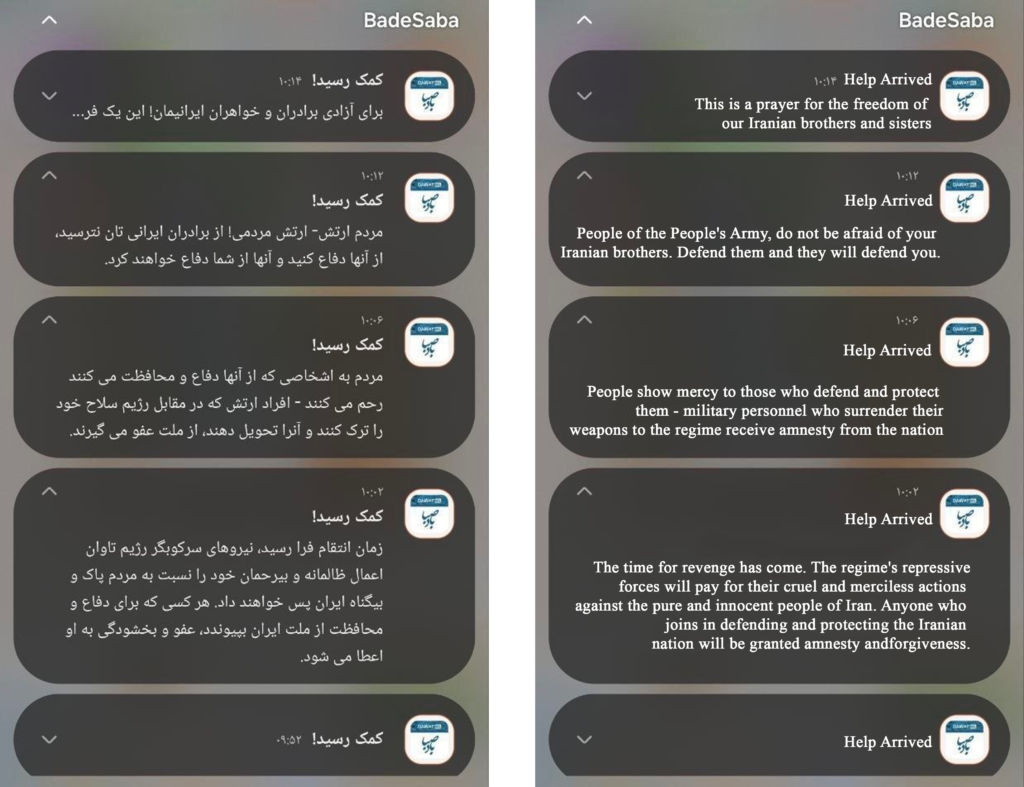
Figure 0.1 the above is the push notification screenshot sourced from social media on the left and the machine translation on the right.
As the situation escalates, both sides are intended on going full swing as most Iranian Hacktivist’s are opting for the great Cyber Campaign, and Western front seems to respond in kind, even the earlier breach of January of Islamic Republic of Iran Broadcasting (IRIB), where for a brief moment, the Anti-regime hacktivists, played the message of Reza Pahlavi, the country’s exiled Crown Prince and called on the people, “You are the national army of Iran, not the Islamic Republic army,” in a brief recording he was apparently seen urging the soldiers to put down their weapons and side with the citizens. The escalating tensions of the real war, is also now spilling over to the digital space, their approach to disable systems, need to be studied for applications, especially since it gauges how strategic use of grey zone vector in cyberspace , modern operations seamlessly combine physical force with digital tactics, i.e. using Big data to process surveillance information for targeting, disabling localized cell towers to blind security details, and weaponizing native applications like the BadeSaba app to bypass state censorship and incite regime change defenders must urgently adapt.
This convergence of the physical and digital warfare is clearly visible. To mitigate the risks of this escalating asymmetric battlefield, security professionals must fortify high-risk sectors against a surge of retaliatory attacks from hacktivist groups deploying wiper malware and DDoS campaigns against critical infrastructure and SCADA systems.
To conclude preparing for future conflicts demands securing vulnerable infrastructure and developing robust contingencies against digital psychological operations.