Introduction
In the world we live in today, data is the most valued commodity available. The society has moved well ahead from mere subsistence and concerned itself with the intricacies of power play and balances. Countries at war, in vain or neutral supporters are all connected through pipeline information. The procurement of these pieces of information can be discrete and secretive. Besides the traditional means of acquisition, that is through espionage, the recent trends have shown a rise in sourcing information through the cyber world. Beyond observable physical domains, cyberspace constitutes an additional arena of strategic competition, which transact data and highly influence various state and non-state activities. Amongst several malware actors one of the most sophisticated and well organised are Advanced Persistent Threats.
Advanced Persistent Threats (APTs)
The general explanation of APTs according to Microsoft in general, is that they are agents/entities comprising of individual and in some instances sponsored by Nation States, whose primary goal is to breach secure networks and embed themselves within the architecture for malicious purposes, the primary aim of such actors, especially in terms of Nation Sponsored APT’s are, information gathering, to maintain persistent access & further escalate their privileges and gain entry to lateral systems, for fulfilling their intent or supplementing it. The modus operandi of these actors can be termed as ‘passive-aggressive’ in nature. They avoid direct confrontation and aim to remain undetected so they can ensure lateral movement and gain access to classified information on their targets. The actors facilitate this infiltration by either external techniques such a trial-and-error method, identifying vulnerabilities in a system or through internal techniques like shoulder surfing or credential theft or advances social engineering tactics. They are typically well funded, involve experienced teams of cybercriminals and target high value organisations/instructions and are not restricted to any individual country. Although there are different types of APTs classified in terms of their motives, this article would be focusing on APTs affecting Nation-States through cyber espionage. On the same line, there have been multiple APTs that have infiltrated into state documents and have essentially caused delay or disruption of state machinery, the paper would be analysing on in particular Salt Typhoon (China), while most famous ones include- Goblin Panda (China), Fancy Bear (Russia), Ocean Buffalo (Vietnam), Helix Kitten (Iran).
Salt Typhoon
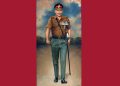
‘Salt Typhoon’, a classification given by Microsoft, is also identified by several organisations as Operator Panda (CrowdStrike), Red Mike (Recorded Future’s Insikt Group), UNC5807 (Mandiant) and Ghost Emperor (Kaspersky Lab). In October 2024, People’s Republic of China’s, government funded cyber team carried out the operation of the Salt Typhoon which infected the telecommunications sector of The United States exposing the vulnerabilities in the infrastructure. Their area of target was, precisely, corporations like Verizon, T-Mobile and AT & T. Through this they fundamentally wanted to gain access to call detail records, such as IP addresses, phone numbers, timestamps, call audio recordings, and surveillance information. China has already been notorious for cyber espionage and reconnaissance, but what made this distinct was that it targeted the global telecommunications sector. Despite measures in place, the American systems failed to detect the prolonged Chinese access to their systems. In order to get the initial access the APT in this particular instance has Exploited Public-Facing Application method for their benefit, the approach involves exploiting publicly known common vulnerabilities and exposures “CVEs” for short, a vulnerability which should have been plugged but remained open allowing persistent access and breach. In this instance the CVEs exploited were,
- CVE-2024-21887 – Ivanti Connect Secure and Ivanti Policy Secure web-component command injection vulnerability, commonly chained after CVE-2023-46805 (authentication bypass).
- CVE-2024-3400 – It allows for unauthenticated remote code execution (RCE) on firewalls when Global Protect is enabled on specific versions/configurations.
- CVE-2023-20273 – Commonly chained with CVE-2023-20198 for initial access to achieve code execution as root
- CVE-2023-20198 – Cisco IOS XE web user interface authentication bypass vulnerability
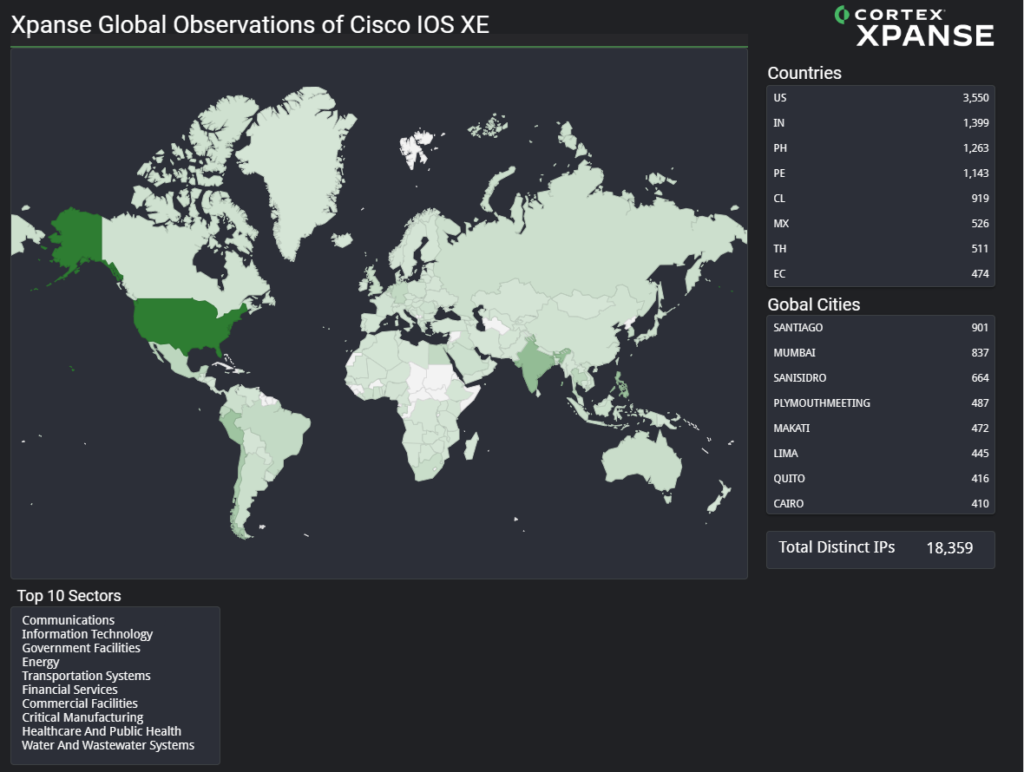
Figure 1: Heatmap displaying global impact of CVE-2023-20198 from Unit 42 Palo Alto Networks
The Point to note is that sufficient advisories detailing said, vulnerabilities were released yet these vulnerabilities were not plugged. In a 2025 Joint Cybersecurity Advisory issued, The TTPs of these Chinese State sponsored actors have been analysed and a trail has been established- China based entities such as Beijing Huanyu Tianqiong Information Technology, Sichuan Zhixin Ruijie Network Technology Co. Ltd., and Sichuan Juxinhe Network Technology Co. Ltd. supply cyber-related goods and services to Chinese intelligence services, which also include several PLO units and the Ministry of State Security. The consequences were not only restricted to the USA but were faced by 80 other countries as well. Even more recently, On 18 July 2025, China based threat actors (UN3886), breached Singapore’s telecommunications sector as well. They used a zero day exploit to bypass the firewall and gained access into the telecom’s networks. This highlights the consistent efforts of the PRC to seep into the system to gain secretive and valuable insights in the activities of the governments across the globe.
The vulnerability that Salt Typhoon exploited was CVE-2023-20198 and CVE-2023-20273, the former exploits web user interface (UI) of Cisco IOS XE and the latter although not as jeopardizing as the former is, allows attackers to carry out commands with root privileges. The attackers get unauthenticated access to the infected systems and are able to exfiltrate data and run commands. The CVE-2023-20273 is often tied to CVE-2023-20198 to maximise impact and gain full control over operations.
Data taken from Shadow Server Service – Stats of CVE-2023-20198 as on 22 February 2026
Although CVE-2023-20198 had been very active in 2023, It still remains a prevalent vulnerability as unpatched and exposed devices remain common. As of 22 February 2026, there are 71 IP addresses which are visible and potentially exploitable.
USA’s countermeasures against Salt Typhoon intrusions
The United States in its immediate response to this systemic breakdown cancelled significant drills and all information was handwritten and hand delivered. After the vulnerability was patched the members of the Congress and Senate called for a meeting on 4th December 2024, where the matter was discussed and the members expressed their concerns on several issues like cyber hygiene and zero day defence monitoring in real time. A document highlighting these implications has been published by the Congressional Research Service (23 January 2025), in which the congressmen and senators unanimously agree on the improved working of the previously established institutions. Rather than burdening the state machinery with new establishments, they worked to empower the already existing- Cyber Unified Coordination Group, Cyber Safety Review Board (CSRB) and called for the increase in preparedness of CyberSecurity and Infrastructure Security Agency (CISA), the Sector Risk Management Agency for the communications sector. The Cyber UCG was to maintain a tandem between the United States government policy with respect to emergence of cyber threats, CSRB arguably shall examine these threats and make reports which would function as learnings for both the public and private sector ; although its existence is subject to debate, and CISA, as it is stated in the aforementioned document shall- prevent, protect, respond and recover from threats.
These boards and councils provide a systemic redressal to cyber threats, but their mere existence does not make the difference. Regular updation and real time monitoring are required for an efficient functioning. The concept of blue team and Red Team however leaps in here. Every system is prone to vulnerabilities and as long as the system functions, there are inherent chances for intrusions (red team), but it is the onus of the state actors to minimize cause and effect by early detection (blue team).
The Indian Arena From the early 2000s, India recognized the significance of virtual spaces and made policies to lay limitations and exemptions. In 2004, the Indian government launched Indian Computer Emergency Response Team (Cert-IN), initially it was launched as an agency dealing with computer security incidents but after an amendment in 2008, its scope widened. Now it analyses, examines and reports cyber security threats regularly. For example, identification of multiple vulnerabilities in Jenkins (20 February 2026). This acts as an informational database which aids the government linked systems to patch the affected systems. Other institutions also function in conjunction such as – Indian Cybercrime Coordination Centre and National Critical Information Infrastructure Protection Centre . These institutions provide a multidimensional approach to combat cyber infiltrations and specialise in areas of coordination and protection respectively.
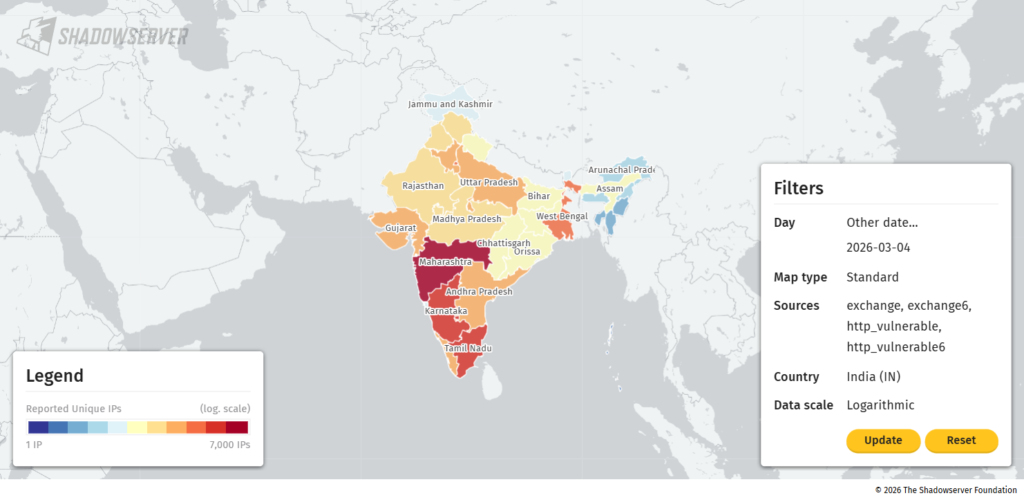
Data from Shadow Server: Vulnerabilities affecting India as on 04th March 2026
The National Technical Research Organization (NTRO) is also an important institution in this discussion. It is a technical intelligence agency under India’s National Security Advisor in the PMO. It aims to gather intelligence through geospatial intelligence, satellite and cyber monitoring. Although the organisation’s financial and procurement activities have been heavily criticised, it still plays a pivotal role in identification of threats and their disposal. The Indian Arena is flooded with new initiatives and Public-Private collaborations, but it requires a steady and consistent implementation to combat cyber space intrusions.
Roadmap to India’s Cyber Security Architecture
India, through diverse legislation, has attempted to combat cybercrimes and foster cyber diplomacy. But due to inherent limitations in the devised structures the efficiency becomes constricted. There is an absence of integrated structures which complicate the setting and develop chaos amongst various institutions. This article aims to propose a policy reform through which this issue along with others is addressed.
CERT IN, comprises Computer Security Incident Response Team for the Finance Sector (CSIRT-Fin) and State CSIRTs. It can further broaden its impact base and function as an umbrella organisation which directs all the institutions and delegates cases for their disposal. The organisations such as NCIIPC, ICCC, Cyber Swacchta Kendra, CSIRT, Public-Private collaborative services may be integrated under the ambit of CERT IN, similar to CISA in the American setting. It shall identify threats and disseminate them to the concerned institutions for specialised attention and steadfast disbursal as due to the pendency of vulnerabilities confidential state data can be under threat. CERT-IN shall function as a repository of cyber data and maintain public catalogues whose information should be updated regularly. Thus, quantitative identification and qualitative disposal become critical when India is placed amongst the superpowers. The National Technical Research Organisation shall be appraised and CERT IN, will report and update to NTRO for easy inflow of information and smooth operation. For all these reforms to come into action, allocation of more funds is required, which will ensure sophisticated and structured functioning of the Indian cyber network.
Conclusion The cyber spaces are dynamic and evolve as new methodologies and technologies come into play. No country can claim vulnerability free devices or patched ports; one can only update and regularly practice cyber hygiene. With these inherent complications, efforts need to be put in preparedness for response to these casualties rather than perfection of devices. USA spending over USD 25 billion annually on Cyber Security reflects the attempt to prioritise protection of information on these virtual spaces. India shall not steer the cyber policies on the same path as that of the United States but shall tailor it to suit the needs of the Indian setting, be it for the fund allocation or the structure of cyber security networks. The roadmap proposed through this article calls for CERT IN to be the anchor of the diverse institutions responsible to counter cyber intrusions. With the emergence of changing nature of threats, such as breach of financial details through the arrival of quantum computers, a redressal mechanism is needed to provide remedial solutions such as Implementation of Quantum Safe Ecosystem, which acknowledge the nature and magnitude of the grievance. Thus, knowledge sharing, real time monitoring and regular updation are the thumb rules of the cyber world where even diplomacy falters.