Introduction
Amidst the ongoing conflict between Iran and Israel, the world is witnessing nation actors, employing Grey Zone Warfare tactics. Iranian threat actors, namely tracked as “APT Iran” attributed to espionage and data exfiltration and “Handala” linked to defacement and psychological operations, are associated with a series of cyber breaches against the state of Israel and the United States with U.S and Israel conducting counteroperations; Israeli operations have been attributed to Unit 8200. SOCRadar has documented the resulting cycle of attack and response in its analysis of the three-party conflict.
Handala is a hacktivist group which has been linked to Iran’s Ministry of Intelligence and Security (MOIS) is claiming credit for the cyberattack against medical technology giant Stryker, the breach of Kash Patel’s personal email, and the exposure of personal details of 28 senior engineers at Lockheed Martin. APT Iran is now claiming to have stolen an extensive dataset from Lockheed Martin, a defence contractor based in the United States, which is now being advertised for sale on the “Threat Market” forum.
This article will make an attempt to analyse the data theft and cyber breaches during the Iran-Israel conflict and address the relation to India’s Atmanirbhar Bharat policy, as Indian technology programs would become intelligence targets as they develop. Groups such as APT Iran and Handala use network intrusions to obtain proprietary data and then seem to sell it on the Darkweb. Such breaches affect nations that base defence and economic strategies on the security of domestic intellectual property.
Cyber Breaches
In early March of 2026, APT Iran, a pro-Iranian hacktivist group, claimed to have acquired 375 terabytes of data from Lockheed Martin, reported by threat intelligence sources on X namely DailyDarkWeb and H4ckmanac were among the first to amplify the claims, sharing screenshots of the alleged 375 TB data dump and details of the $400 million ransom demand an aerospace, defence, and security datasets of Lockheed Martin. The highly classified data was later found available for sale on a dark web marketplace named “Threat Market.” After further digging by CLAWS, researcher’s the onion link for the same was located and as under
http://hi6bo2aihmuzkaj6gi6sigmut5bcwvguqpma3hwxsjfbqsccnchmybid.onion
* Note: the link was opened in Tor Browser
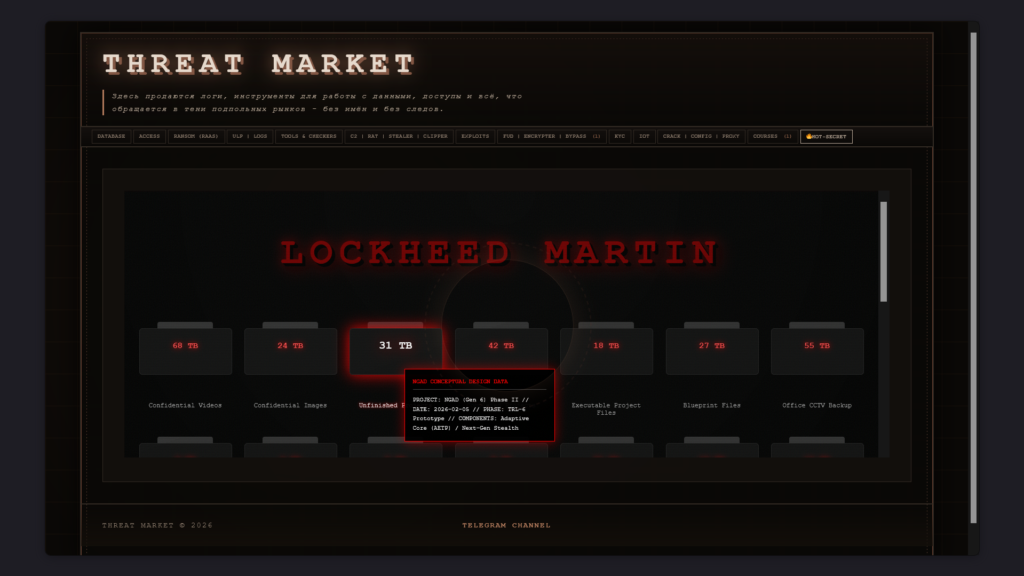
Figure 01: Screenshot from Threat Market, as seen above F-35 Data is on sale
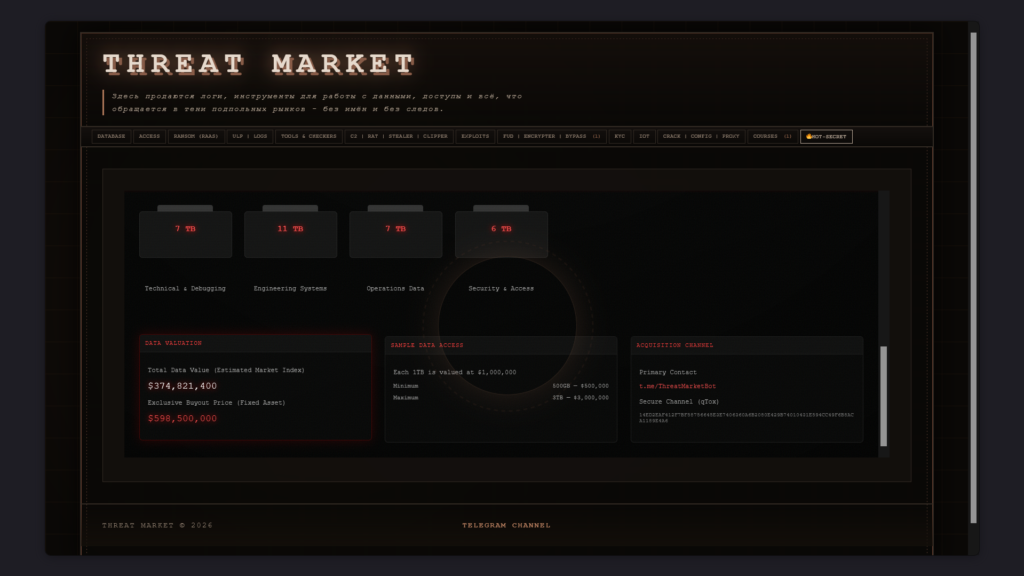
Figure 02: Screenshot from Threat Market, the total valuation is held at $ 374,821,400
The platform named “Threat Market” clearly shows the Lockheed Martin page, where various sensitive files are listed for sale, with their units mentioned. These available files are categorized as “Confidential Videos,” “Confidential Images,” “Office CCTV Backup,” “Source Codes,” and “Security & Access.” The hackers claim that the data includes blueprints of the F-35 fighter jet, a 5th generation American fighter jet and contracts of the company with the Pentagon. This implies deep access into the company’s operating systems and access to sensitive information. The total value mentioned for the complete dataset is roughly $374 million ($374,821,400), and the exclusive buyout price is close to $600 million ($598,500,000). Sample data is also available, where 1 TB is valued at $1,000,000. As these sites are hosted on the The onion network, they are virtually, impossible to trace, or track since, the network has multiple layer’s and hence cannot be traced by traditional methods.
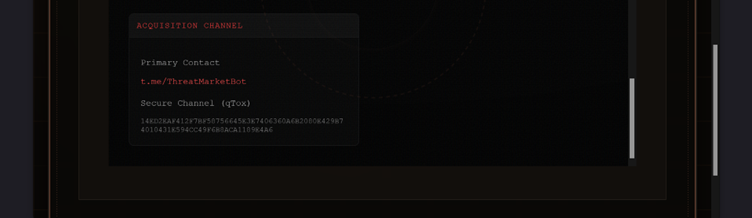
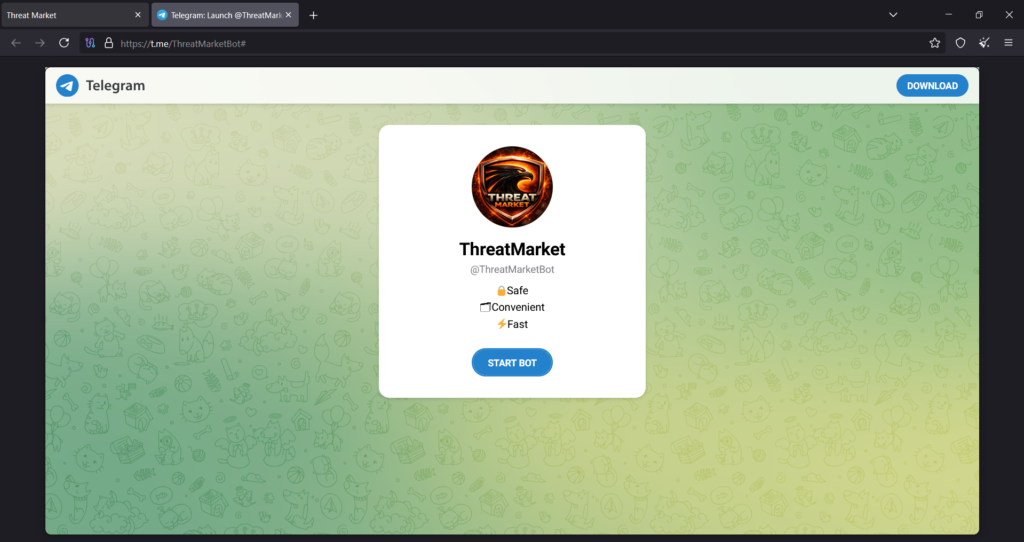
The threat group has provided a Telegram channel, “t.me/ThreatMarketBot,” as their primary contact; its “Secret Chat” feature offers E2EE that is inaccessible to both service providers and law enforcement.
A secure qTox link
“14ED2EAF412F7BF58756645E3E7406360A6B2080E429B74010431E594CC49F6B8ACA1189E4A6”
is also provided for communication regarding the deal. It is a secure messaging platform based on the Tox protocol for encrypted conversations with clients and offers interactions with high-security features, including encryption for text, voice, video, and file sharing, with no central servers. Tox, when operated through Tor, can hide IP addresses and locations, virtually leaveing no trace of the communication and keeping conversations highly secure and untraceable.
Both “Threat Market” is being utilized to publicize threats, demand ransoms, and facilitate announcements and conversations.
The transactions will take place through cryptocurrency, as there is no central bank or government that can freeze a hacker’s account or block access to funds. This allows criminals to bypass international sanctions and legal restrictions.
The authenticity of the claims made by APT Iran about the Lockheed Martin data leak and the scale of the breach remain unverified but even the possibility of the leak holds major geopolitical consequences.
If the claims are accurate, the exposure of F-35 fighter jet blueprints could lead to significant intellectual property loss and can even become a leverage point for hostile nations to develop countermeasures by exploiting the weaknesses of the fighter jets, even more so, they could integrate it to their improve their own models.
The Threat Market page contains files of “Source Code,” “Defence Contract,” “Defence System,” “Blueprint File,” and “F-35 Block 4 Full Project.” Block 4 is an upgrade phase of the military aircraft F-35, designed to significantly expand its combat capabilities, sensors, and software. Through blueprints, loopholes can be identified which can be utilized to hack or sabotage the operating systems of the F-35.
Companies that build military weapons, manage military logistics, maintain satellite communications, or provide IT infrastructure to military agencies are critical, as hackers can disrupt the supply chains feeding the military campaign. It can extend the timeline of the war, increase costs, and potentially force operational changes in the field.
Reverse engineering becomes a major threat, as China is noted for it, it has partially happened with jets like the Chinese Chengdu J-20.
India does not operate the F-35 fighter jet, so it does not have any direct impact from the data leak event, but if sensitive data related to military technology is leaked, it may lead to geopolitical instability.
In a Telegram post by ATP Iran, it was mentioned that the group has been receiving numerous requests from China, Russia, and Arab countries to sell this information to them, and some of them are even willing to pay for sample data. If China gets access to the sensitive data related to the fighter jets, it may reverse engineer it to develop similar technology, which may become a combat threat to India’s defence strategies. As of 2026, India does not own any operational fifth-generation aircraft in its air force; as a result, India will have to re-evaluate its air defence strategies.
This breach reflects that cyberattacks are now part of hybrid warfare. Hackers target defence contractors and critical infrastructure. Indian defence public sector undertakings like Hindustan Aeronautics Limited and DRDO-linked vendors should beware of such events, as Chinese and Pakistani threat actors are constantly targeting Indian government organizations in cyber warfare.
India and the US have growing defence ties. Agreements like COMCASA and BECA are signed for military communication, technology sharing, and joint exercises; a data leak of military equipment affects these defence collaborations. These events indicate a “cyber cold war” where the distinction between wartime and peacetime becomes increasingly blurred, and maintaining national security becomes more challenging alongside the growing sophistication of cyber threats in the defence ecosystem, The concern is even more so since India is furthering into the Atmanirbharta Ecosystem, developing indigenous tech while collaborating with foreign countries, to further our goals.